Tailored Corporate Safety Solutions for Your Distinct Company Requirements
In today's progressively intricate organization landscape, making sure the protection and security of your company is of vital significance., we identify that every service has its own special set of safety demands. That is why we supply customized company protection services developed to attend to the certain challenges and susceptabilities of your business.
Evaluating Your Details Security Needs
To effectively resolve your organization's safety and security concerns, it is critical to perform a comprehensive assessment of your specific safety requirements. Comprehending the distinct risks and susceptabilities that your organization encounters is essential for establishing an effective safety and security strategy. Without a correct evaluation, you may allot resources inefficiently or forget essential locations of vulnerability.
The initial step in assessing your certain protection demands is to carry out a complete evaluation of your physical properties, including structures, car park locations, and gain access to points. This examination should recognize possible weaknesses such as inadequate lights, out-of-date safety and security systems, or vulnerable entrance factors. In addition, it is very important to evaluate your company's digital safety and security by evaluating your network framework, data storage, and security procedures. This will assist determine prospective susceptabilities in your IT systems and determine the necessary steps to guard sensitive information.
Another important aspect of assessing your protection needs is comprehending your organization's unique functional requirements and compliance responsibilities. This consists of considering variables such as the nature of your industry, the value of your properties, and any kind of regulative or lawful needs that may apply. By comprehending these specific variables, you can tailor your safety gauges to meet the certain demands of your organization.
Tailoring Surveillance Equipments for Optimum Protection
Tailor your surveillance systems to supply optimal security for your service. A one-size-fits-all method simply will not be enough when it comes to protecting your company and its properties. Every organization has its own one-of-a-kind security requirements, and personalizing your surveillance systems is key to guaranteeing that you have the most reliable defense in position.
Firstly, it is essential to carry out a thorough evaluation of your properties to identify vulnerable locations and prospective security risks. This will certainly help determine the kind and number of cams needed, along with their critical positioning. High-risk locations such as entrances, car park, and storage centers may call for more advanced surveillance innovation, such as high-resolution video cameras or evening vision capabilities.

Integrating your surveillance systems with other safety steps, such as accessibility control systems or alarm, can further boost the effectiveness of your total security approach. By customizing your security systems to straighten with your certain company needs, you can have assurance recognizing that your assets, staff members, and clients are protected to the maximum level possible.
Implementing Tailored Gain Access To Control Steps
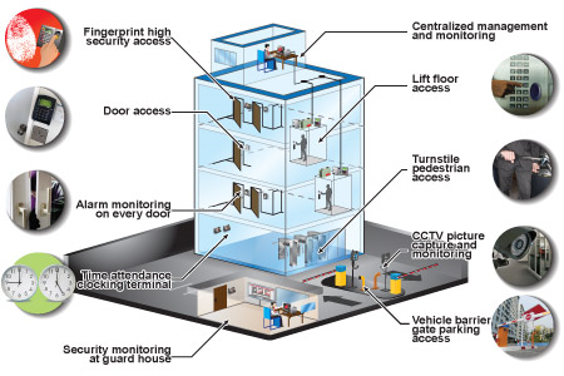
For optimum safety, business must carry out tailored access control measures that straighten with their special business needs. Gain access to control steps are crucial in protecting sensitive details and making certain that just accredited individuals have access to details locations or sources within a company. By tailoring accessibility control steps, companies can see post develop a robust protection system that successfully reduces safeguards and threats their possessions.
Implementing customized access control actions includes several crucial steps. First, an extensive assessment of the firm's safety requirements and prospective vulnerabilities is required. This evaluation should consider elements such as the nature of the company, the worth of the information or possessions being secured, and any regulatory or compliance requirements. Based on this analysis, companies can after that establish the appropriate access control devices to execute.
Access control procedures can consist of a combination of physical controls, such as keycards or badges, along with technological services like biometric authentication or multi-factor verification. These actions can be applied across numerous entrance points, such as doors, gateways, or computer system systems, relying on the company's particular needs.
Additionally, firms have to develop clear plans and treatments regarding gain access to control. This consists of specifying responsibilities and functions, establishing user gain access to degrees, regularly evaluating gain access to benefits, and keeping track of accessibility logs for any type of suspicious activities. Routine training and recognition programs ought to additionally be performed to guarantee employees are aware of the relevance of access control and abide by established methods.
Enhancing Cybersecurity to Secure Sensitive Data
Carrying out robust cybersecurity steps is crucial to successfully safeguard delicate data within a company. In today's electronic landscape, where cyber risks are ending up being significantly innovative, services need to focus on the defense of their useful details. Cybersecurity encompasses a variety of methods and technologies that intend to avoid unauthorized access, data breaches, and various other harmful activities.
To improve cybersecurity and safeguard sensitive information, companies ought to implement a multi-layered approach. In addition, implementing strong gain access to controls, such as multi-factor verification, can assist protect against unapproved accessibility to delicate systems and details.
Furthermore, companies must have an event response plan in position to successfully react to and minimize any cybersecurity cases. This plan ought to lay out the steps to be absorbed the event of a data violation or cyber strike, including communication protocols, containment steps, and healing methods.
Recurring Support and Maintenance for Your One-of-a-kind Needs
To guarantee the continued effectiveness of cybersecurity procedures, continuous assistance and maintenance are important for addressing the developing dangers encountered by companies in securing their delicate information. In today's quickly changing digital landscape, cybercriminals are frequently locating new ways to make use of vulnerabilities and violation safety systems. It is critical for companies to have a durable assistance and maintenance system in place to remain ahead of these risks and protect their useful details.
Continuous assistance and maintenance involve frequently patching and updating protection software program, checking network tasks, and performing vulnerability evaluations to recognize any type of weak points in the system. It additionally consists of supplying timely assistance and guidance to workers in implementing safety best techniques and replying to potential safety incidents.
By spending in ongoing support and upkeep services, services can benefit from basics aggressive surveillance and detection of prospective threats, as well as prompt feedback and removal in the event of a protection breach. This not only assists in reducing the impact of an assault but additionally ensures that the organization's security posture continues to be adaptable and solid to the developing threat landscape.
Conclusion

To successfully address your company's safety concerns, it is essential to perform a thorough analysis of your particular safety needs. Every service has its very own one-of-a-kind protection needs, and customizing your surveillance systems is crucial to making certain that you have the most reliable security in area.
For ideal safety and security, firms need to carry out tailored access control steps that line up with their distinct service needs.In verdict, tailored corporate safety options are essential for companies to resolve their special safety requirements. By analyzing particular safety and security needs, personalizing monitoring systems, implementing customized access control measures, and boosting cybersecurity, companies can protect sensitive information and protect against possible risks.